Oracle SAML
Learn how to configure a connection to Oracle via SAML.
Each SSO Identity Provider requires specific information to create and configure a new connection. Often, the information required to create a connection will differ by Identity Provider.
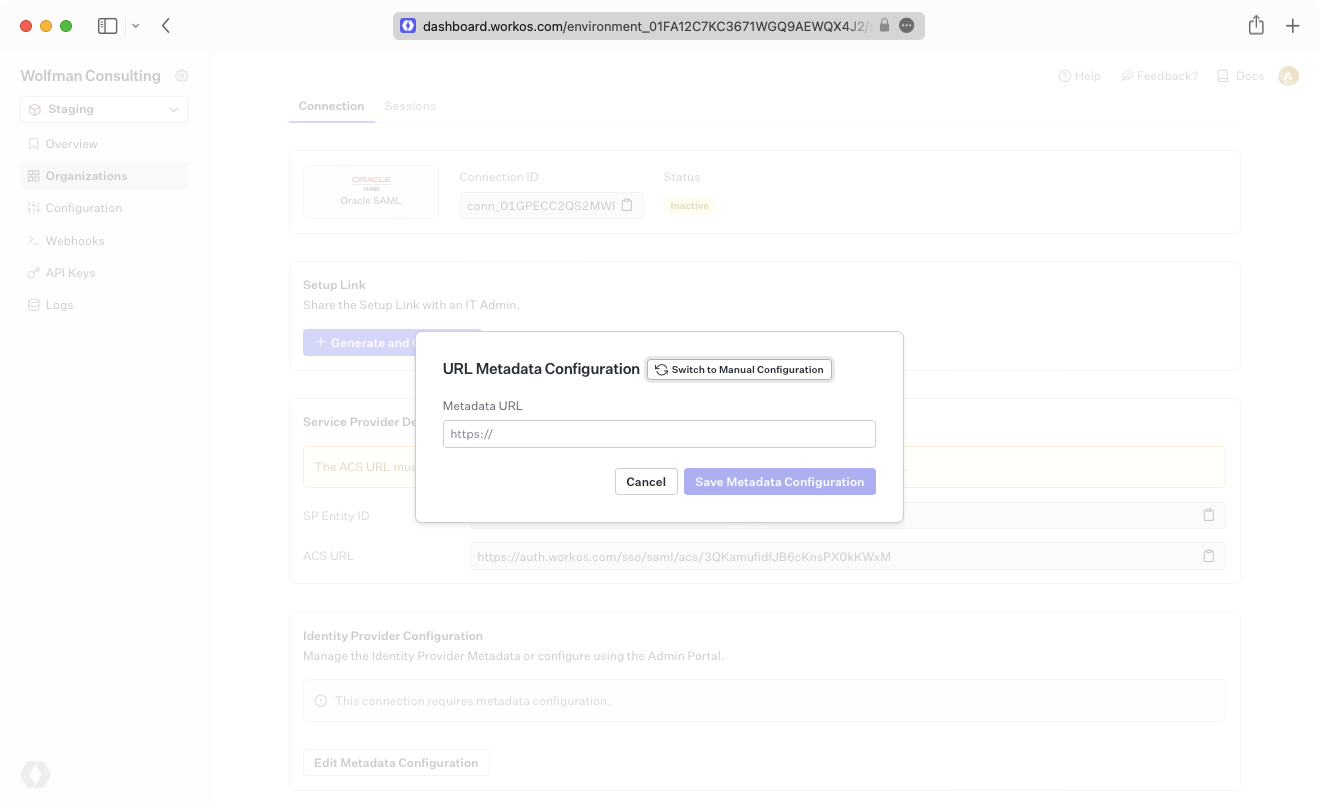
To create an Oracle SAML connection, you’ll need the Identity Provider Metadata URL that is available from the organization’s Oracle SAML instance.
WorkOS provides the ACS URL and the SP Entity ID. They are readily available in your connection Settings in the WorkOS Dashboard.
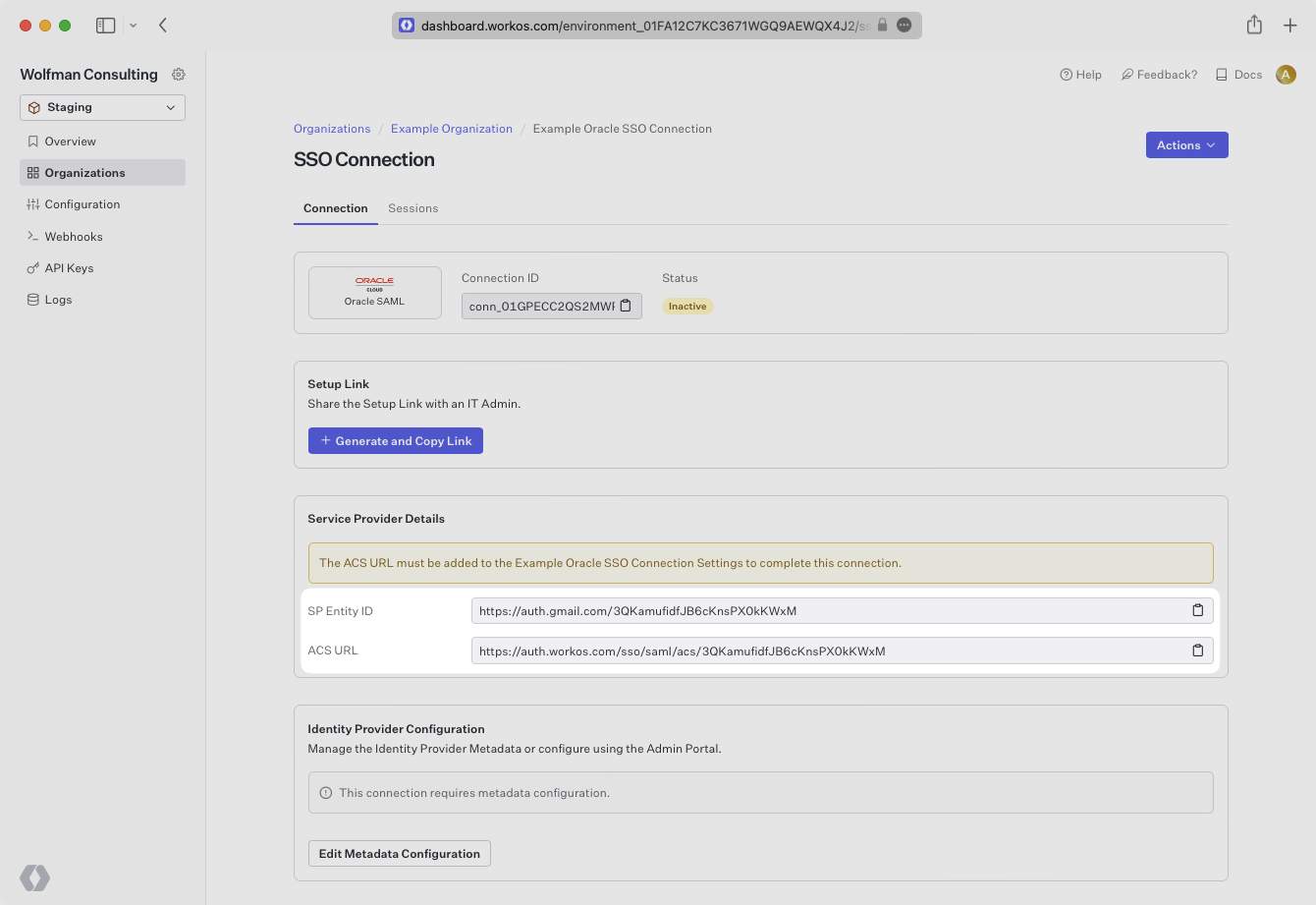
The ACS URL is the location an Identity Provider redirects its authentication response to. The SP Entity ID is a URI used to identify the issuer of a SAML request, response, or assertion.
In order to integrate you’ll need the IdP Metadata URL.
Normally, this will come from the organization’s IT management team when they set up your application’s SAML configuration in their Oracle instance. But, should that not be the case during your setup, here’s how to obtain it.
Follow the Oracle Cloud documentation to create a new SAML application.
Copy and paste the ACS URL and SP Entity ID into the corresponding fields for Service Provider details and configuration.
In the Advanced Settings of the SSO Configuration page, ensure that you select Signed SSO for Assertion and Response, and Include Signing Certificate in Signature.
Expand the Attribute Configuration section on the SSO Configuration page and add the following 4 required attributes: firstName, lastName, email, and id.
Ensure the following attribute mapping is set:
- A user’s first name →
firstName - A user’s last name →
lastName - A user’s email address →
email - A unique identifier representing a user →
id
With identity provider role assignment, users can receive roles within your application based on their group memberships. To return this information in the attribute statement, map the groups in your identity provider to a SAML attribute named groups.
Finish role assignment set-up by navigating to the SSO connection page in the Organization section of the WorkOS Dashboard. Create SSO groups by referencing the group IdP ID. Then, assign roles to these SSO groups so group members are automatically granted roles within your application.
Obtain the IdP Metadata URL following the instructions from Oracle.
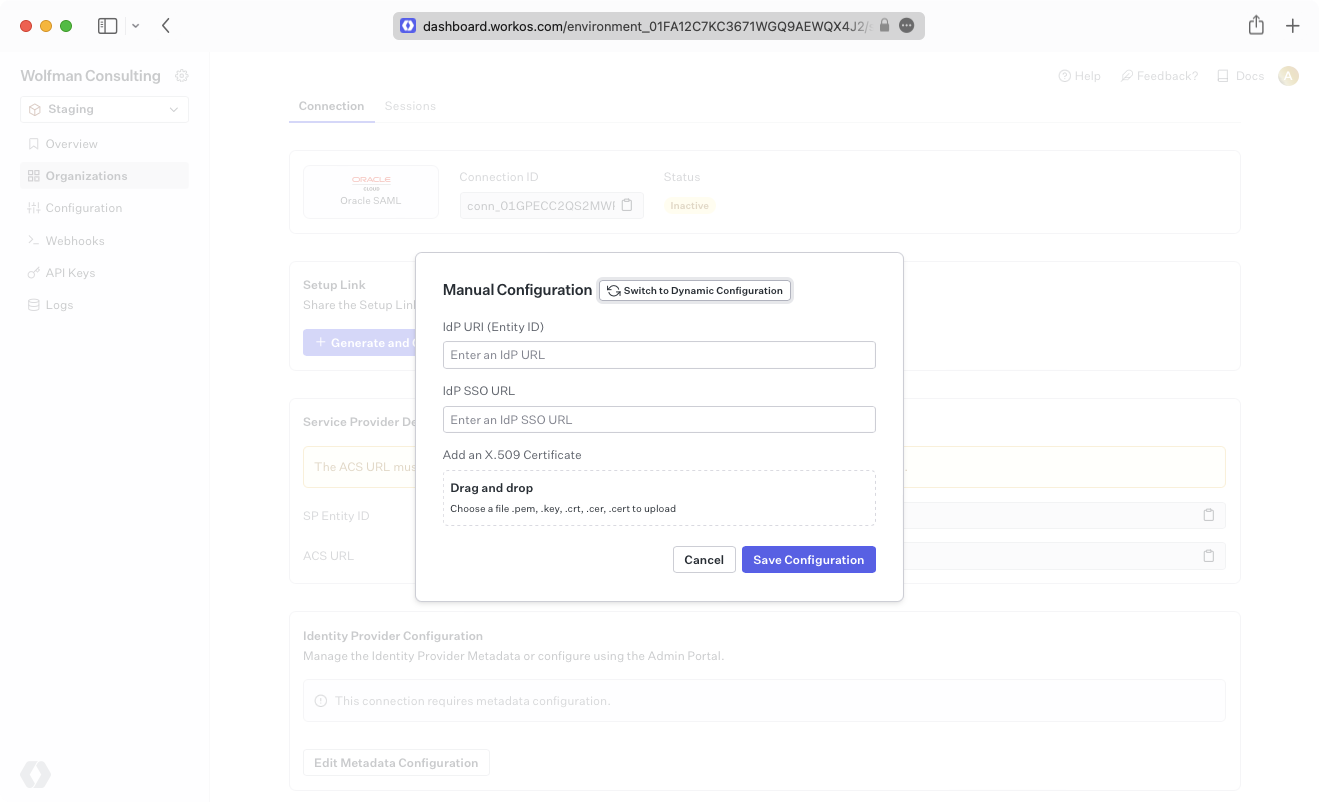
Alternatively, you can manually configure the connection by providing the IdP URI (Entity ID), IdP SSO URL and X.509 Certificate.
Your connection will then be Active and good to go!