What it takes to get FedRAMP authorized: Lessons from companies that did it
What it really takes to sell to the U.S. government, from the teams who have been through it.
For software companies that want to sell to the U.S. federal government, FedRAMP authorization is the front door. It is also, historically, one of the most expensive doors in enterprise software to walk through. A conventional authorization runs 12 to 18 months for teams that arrive prepared and stretches past 24 months for teams that do not, with initial investment that can exceed $1 million before a single government contract is signed.
The program is changing. FedRAMP 20x, launched in March 2025, is pushing the process toward automation and continuous validation, and early pilot participants have reached authorization in as little as three months. But most of today's authorized products live under the legacy Rev5 baseline, which is what the vast majority of FedRAMP-authorized SaaS companies actually built toward. Understanding how those companies cleared the bar, and what it cost them, is the best way to plan a credible authorization effort of your own.
FedRAMP 101
FedRAMP, short for the Federal Risk and Authorization Management Program, is the security authorization that U.S. federal agencies require before they can use a cloud product. If you want a civilian agency or the Department of Defense as a customer, you need it, and there are no exceptions for commercial software.
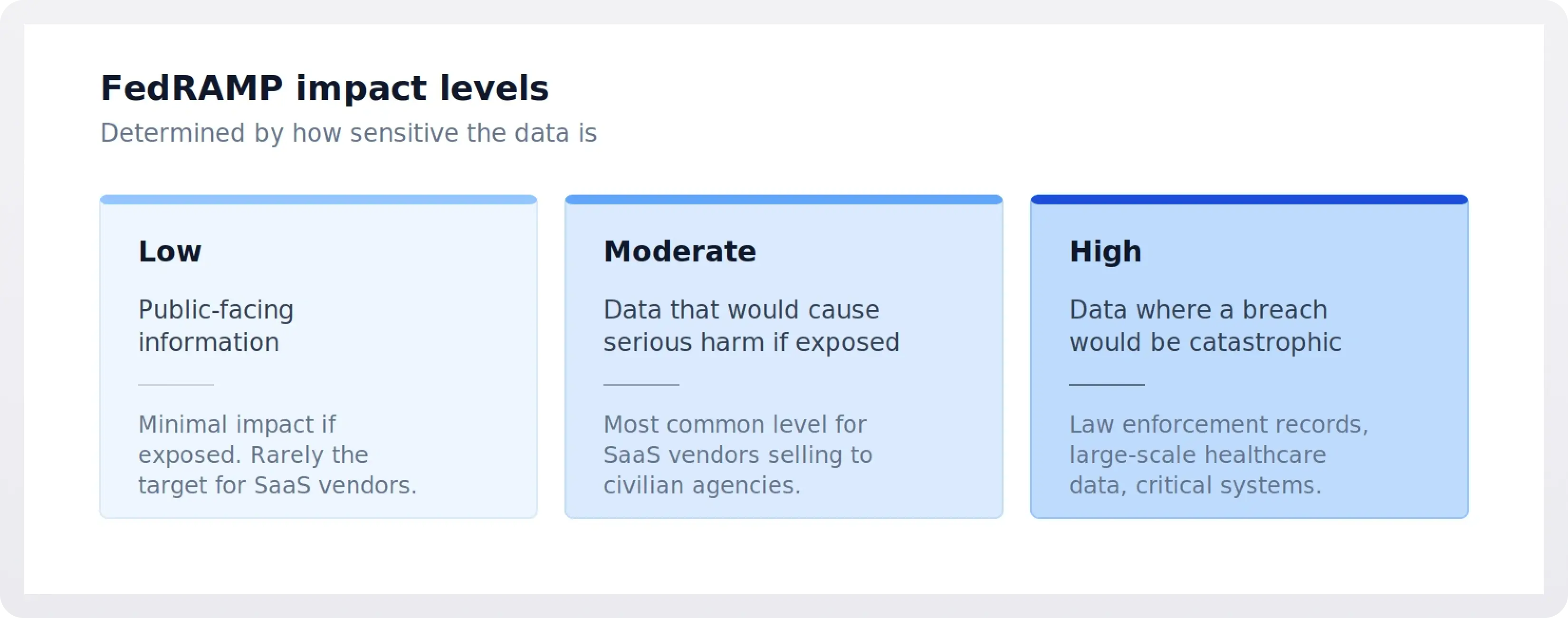
The program has three impact levels based on how sensitive the data is:
- Low covers public-facing information.
- Moderate, the most common level for SaaS vendors, covers data that would cause serious harm if exposed.
- High covers data where a breach would be catastrophic, such as law enforcement records or large-scale healthcare data.
Two paths to authorization exist today.
- Rev5 is the traditional path, built around the NIST SP 800-53 Revision 5 control catalog and long written documentation.
- FedRAMP 20x is the new path, launched in 2025, built around automated evidence and continuous validation.
Both paths land in the same place: an Authority to Operate, or ATO, issued by a federal agency. That is what "FedRAMP authorized" means in practice.
What FedRAMP actually demands
The headline costs and timelines are only part of the story. Most engineering teams underestimate four things: the authorization boundary, the 3PAO relationship, the agency sponsorship process, and continuous monitoring.
- The authorization boundary defines what is in scope. Everything inside must meet FedRAMP requirements, and everything outside must be documented as an external dependency. Drawing this boundary correctly, once, is one of the highest-leverage decisions in the whole program. Novastraxis, which went through FedRAMP High, has written publicly about defining its boundary too broadly at the start and then having to rework its System Security Plan six months in. The advice that came out of that experience: keep the boundary as small as possible while still covering the services your government customers actually need.
- The 3PAO, or Third Party Assessment Organization, runs the independent audit. Not every 3PAO is good at every kind of environment. Teams running cloud-native stacks (Kubernetes, microservices, serverless) have reported that some assessors are still primarily experienced with traditional datacenter environments and struggle to map modern architectures onto NIST 800-53 control families. Choosing a 3PAO with real experience in your architecture matters more than price.
- Agency sponsorship is the step that trips up many first-time applicants. For most paths to authorization, a federal agency has to commit to sponsor the cloud service and eventually issue the Authority to Operate. For vendors without existing federal relationships, finding that sponsor can take months or longer. The alternative until recently was the Joint Authorization Board, which was discontinued as part of the 2024 policy overhaul.
- Continuous monitoring is where the work becomes permanent, and it is the phase where most teams underestimate the ongoing cost. Monthly vulnerability scans, annual assessments, Plan of Action and Milestones (POA&M) updates, and Significant Change Request submissions for any material system change. None of this goes away once the Authority to Operate is issued. Treating ConMon as a project that ends at authorization, rather than a permanent operating model, is the single most common reason companies struggle in year two.
Wiz: Risk first, not checklist first
Wiz published a detailed account of its path to FedRAMP High, and it is one of the clearest recent examples of how a cloud-native company can compress the timeline without cutting corners. The core idea in the Wiz playbook is that FedRAMP works better as a risk-prioritization exercise than as a compliance checklist. Rather than treating each control as an isolated line item, Wiz organized its work around a three-stage risk model:
- proactive (complete visibility into cloud resources and identities),
- preventative (shifting security assessment left into the software development lifecycle), and
- reactive (incident response that already has root cause and blast radius context).
The practical result was that Wiz stopped treating POA&M entries as a flat list of CVEs. Instead, it prioritized remediation based on where a vulnerability actually sat in the system. A low-CVSS vulnerability on a sensitive internal asset might be higher priority than a high-CVSS vulnerability on a non-public one without sensitive data. That context is what allowed the team to document and defend risk decisions during the assessment, and it reduced the manual burden of continuous monitoring after authorization.
Wiz also sequenced the work in a way that kept product velocity intact. It achieved FedRAMP Moderate first, then used Significant Change Requests to bring its government offering toward feature parity with the commercial product while simultaneously uplifting to High under an agency-sponsored authorization. The uplift from Moderate to High is usually treated as a second climb. By keeping the underlying risk model consistent, Wiz was able to treat it more like a delta.
The ConMon payoff is where the risk-first approach really shows its value. Rather than treating asset inventory as a list of virtual machines to reconcile each month, Wiz built visibility across four dimensions: identities (who has access), workloads (what is running), data (where the sensitive information lives), and network (how it is exposed). That structure is what lets the team identify toxic combinations automatically, rather than manually correlating scan results in spreadsheets. The team has publicly credited this model with turning what is traditionally "audit time" into normal operating time.
GitLab: The agency-sponsored Moderate path
GitLab's journey is a good example of the conventional Rev5 path run well. The company announced its FedRAMP "In Process" designation at the Moderate impact level in June 2024, listed on the FedRAMP Marketplace, and achieved full Authority to Operate at Moderate in May 2025 under sponsorship from the General Services Administration. The product that carried the authorization was GitLab Dedicated for Government, a new single-tenant managed SaaS offering with data residency, isolation, and private networking designed specifically for federal requirements.
Two things stand out about GitLab's approach. First, they created a dedicated offering rather than trying to stretch their commercial multi-tenant SaaS to meet federal requirements. This is a pattern across most successful FedRAMP efforts. A separate deployment with a separate boundary, often on a different cloud region, is almost always easier than trying to certify the existing commercial environment. Second, the timeline from "In Process" to "Authorized" ran about eleven months, which is on the faster end of the typical range and reflects both a strong agency relationship and mature pre-existing compliance work.
Databricks: Stacking authorizations for the federal market
Databricks took a different approach by building a portfolio of authorizations across clouds and impact levels. The company already held FedRAMP Moderate on AWS commercial regions and FedRAMP High plus DoD Impact Level 5 on Azure when, in February 2025, it added FedRAMP High authorization for its Data Intelligence Platform on AWS GovCloud. That authorization came from the FedRAMP Program Management Office itself.
The Databricks pattern illustrates a reality many companies run into once they start selling into the public sector. Different customer communities require different authorizations. Civilian agencies want FedRAMP Moderate or High, the Department of Defense wants IL4, IL5, or higher, and intelligence customers want still more. Each authorization adds cost but also expands the addressable market. Databricks stood up a dedicated Public Sector business unit and a Databricks Federal board structure to sustain this long-term investment.
Beyond Identity and the startup reality
Beyond Identity, a cybersecurity startup, published a candid post-mortem on what FedRAMP Moderate cost it as a smaller company. The team's public guidance: validate the market opportunity first, confirm executive sponsorship, and look for a clear 10x return rather than treating FedRAMP as a nice-to-have credential. The numbers Beyond Identity cited roughly match what other sources report for startup-scale efforts: initial investment above $1 million and timelines past 12 months.
The hard problems Beyond Identity flagged are the same ones that show up in almost every FedRAMP post-mortem. Interpreting Moderate controls without clear guidance. Defining authorization boundaries across microservices and shared components. Operationalizing DevSecOps gates that enforce security without stalling development. Picking and integrating SAST, DAST, SBOM, and SCA tooling. None of these are surface-level compliance tasks, and all of them touch engineering in ways that change how teams ship.
What FedRAMP 20x changed, and did not change
FedRAMP 20x, announced in March 2025, is the first structural overhaul of the program in more than a decade. It replaces long narrative documentation with Key Security Indicators (KSIs), which are machine-readable, continuously validated signals of a system's security posture. Program authorization, meaning no agency sponsor is required for the new path, opens a door that was previously closed to many smaller providers.
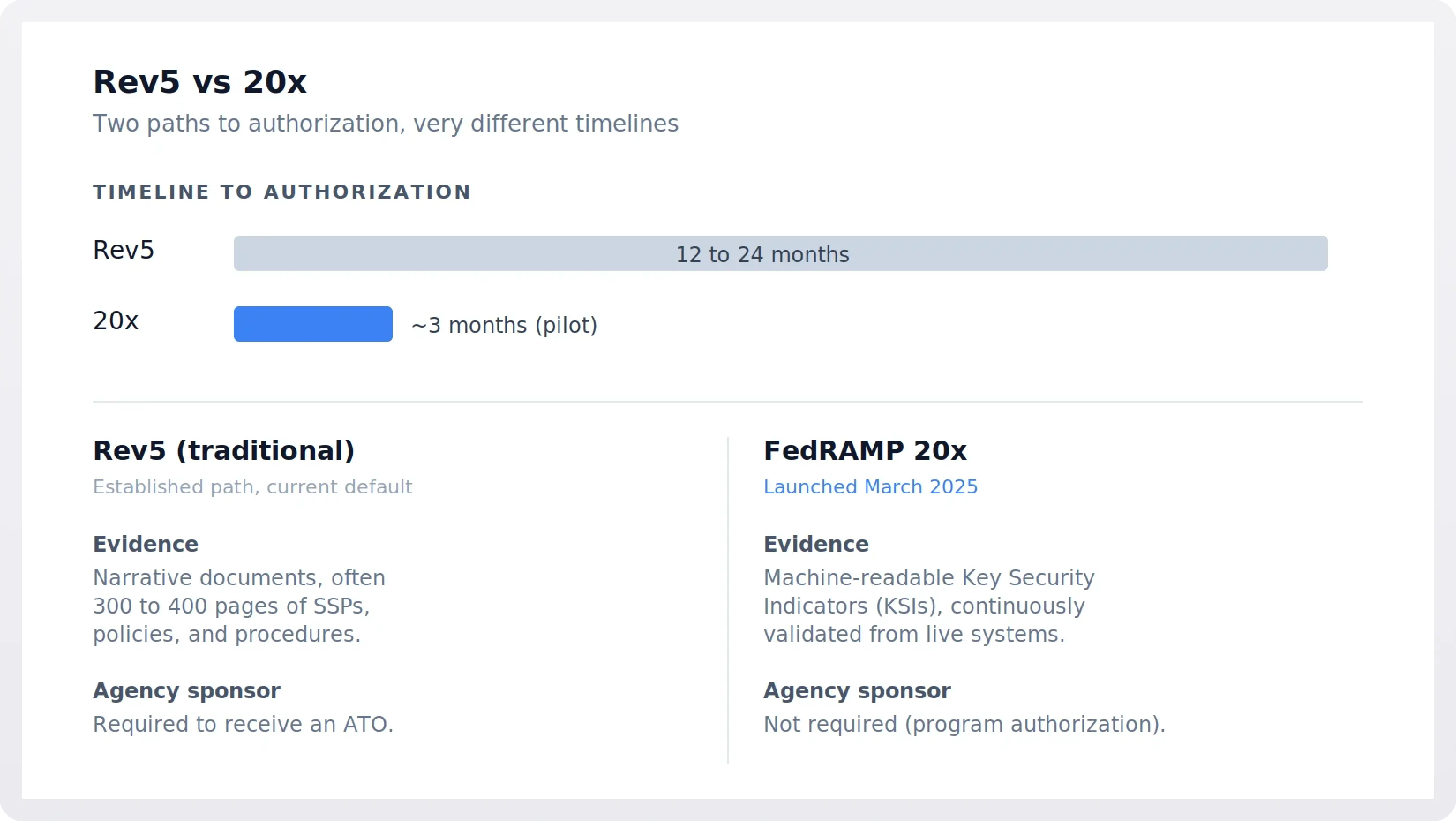
The early results are striking. The Phase 1 pilot ran from April to September 2025 and produced 13 authorizations from 26 submissions, with some providers reaching authorization in roughly three months. Secureframe was among the authorized providers in that cohort. Phase 2, focused on Moderate, began in November 2025 with 13 pilot participants selected across two cohorts and is scheduled to wrap at the end of March 2026. Wide-scale adoption of 20x Low and Moderate is projected for the second half of 2026.
What FedRAMP 20x has not changed is the underlying security maturity required. If anything, automation-first validation raises the bar. The direction of travel across both paths, Rev5 and 20x, is toward continuous validation rather than point-in-time snapshots, a shift that aligns with Executive Order 14028 and broader federal cybersecurity policy. Companies with modern cloud-native architectures, infrastructure-as-code, and automated evidence collection are well positioned for that future. Companies that rely on manual controls and static documentation are not, regardless of which path they choose.
Common patterns from companies that made it
A few things come up consistently in the accounts of companies that have earned FedRAMP authorization.
- Hire someone who has done this before. Multiple teams, including Novastraxis, have pointed out that running a FedRAMP program with only an existing GRC team slows everything down. A full-time program manager with direct FedRAMP PMO experience pays for themselves quickly.
- Engage the FedRAMP PMO early. The program office runs intake meetings, offers readiness guidance, and is generally more accessible than companies expect. Establishing that relationship before the formal assessment prevents timeline surprises.
- Do an honest gap assessment before committing. Companies starting from scratch against the NIST 800-53 High baseline can face a 24 to 36 month runway. Companies with mature SOC 2 and ISO 27001 programs can usually get to authorization in 12 to 18 months. Knowing which of those you are matters more than any vendor pitch.
- Build a dedicated offering, not a stretched version of your commercial product. Isolated environments on GovCloud or Azure Government, with their own boundaries, are almost universally easier to authorize than multi-tenant commercial environments.
- Treat continuous monitoring as a product commitment, not a project. Monthly scans, POA&M upkeep, and Significant Change Requests become part of the engineering cadence forever. Automating evidence collection from day one is cheaper than retrofitting it later.
The bottom line
FedRAMP is still one of the most demanding certifications in enterprise software, and nothing about the 20x rollout changes the fundamental requirement for security maturity. What the recent authorizations do show is that the process no longer has to consume multiple years and derail roadmaps. Companies that treat FedRAMP as a risk program, pick the right 3PAO, scope the boundary tightly, and invest in automation have compressed timelines substantially. The federal market pays for that discipline, but only for the companies that have actually done the work.
Sources
- Wiz, "The Agile FedRAMP Playbook, Part 1"
- Wiz, "The Agile FedRAMP Playbook, Part 2: Continuous Monitoring"
- GitLab, "GitLab Achieves FedRAMP Moderate Authorization" (May 2025)
- Databricks, "Databricks Achieves FedRAMP High Authorization for AWS GovCloud" (February 2025)
- Beyond Identity / The Hacker News, "FedRAMP at Startup Speed: Lessons Learned" (June 2025)
- Novastraxis, "Our FedRAMP High Authorization Journey"
- FedRAMP PMO, "FedRAMP 20x Phase One" and "Phase Two" overviews
- Secureframe, "The FedRAMP 20x Phase Two Moderate Pilot Explained" (January 2026)
- Federal News Network, "FedRAMP 20x pilot finds initial success" (August 2025)