x402 vs. Stripe MPP: How to choose payment infrastructure for AI agents and MCP tools in 2026
A practical comparison of the two protocols reshaping how agents pay for services in 2026.
Until recently, there was really only one way to charge for an API: Stripe subscriptions, API keys, and monthly invoices. That model works fine when a human developer is the one signing up. But AI agents don't fill out forms, and they don't manage billing dashboards.
Two new protocols are competing to solve this:
- Coinbase's x402 embeds payment directly into HTTP requests, with no accounts and no setup.
- Stripe's Machine Payments Protocol (MPP), launched on March 18, 2026 with Tempo, takes a different approach: session-based streaming payments with Stripe's compliance stack built in.
If you're building or monetizing MCP tools, this is now the decision you need to make. This article walks through both protocols in detail, compares them on developer experience, cost, security, and ecosystem maturity, and covers where traditional billing still fits in.
Why traditional billing doesn't work for AI agents
AI agents are getting remarkably good at doing things on our behalf: calling APIs, querying databases, orchestrating multi-step workflows. But the moment an agent needs to pay for a service it hasn't been pre-configured to use, the whole experience breaks down.
The traditional flow (register an account, generate API keys, configure billing, manage subscriptions) was designed for humans with browsers. It requires someone to create a customer account, enter a credit card, and manage a dashboard. Autonomous agents can't do any of that. And the cost structure doesn't fit either: Stripe's standard card processing fee of ~2.9% + $0.30 per transaction makes anything under roughly $1 uneconomical for per-request billing. When your MCP tool charges $0.01 per call, a $0.30 fixed fee is a non-starter.
Traditional billing still has its place. Subscriptions, enterprise contracts, invoicing, compliance: these aren't going away. If you're selling to human teams who want dashboards and receipts, Stripe's core platform remains the best option. We'll come back to where it fits at the end of this article.
But for the agent-native use case (autonomous discovery, per-request micropayments, no human in the loop), the real choice in 2026 is between two purpose-built protocols: x402 and Stripe's MPP.
x402: The open, simple one
x402 is an open protocol (Apache 2.0, governed by the x402 Foundation co-founded by Coinbase and Cloudflare) that repurposes the long-dormant HTTP 402 ("Payment Required") status code. The flow is minimal:
- A client requests a protected resource.
- The server responds with
HTTP 402and machine-readable payment instructions (price, token, chain, recipient wallet). - The client pays on-chain (typically USDC on Base or Solana), attaches proof to a retry request.
- The server verifies settlement and delivers the response.
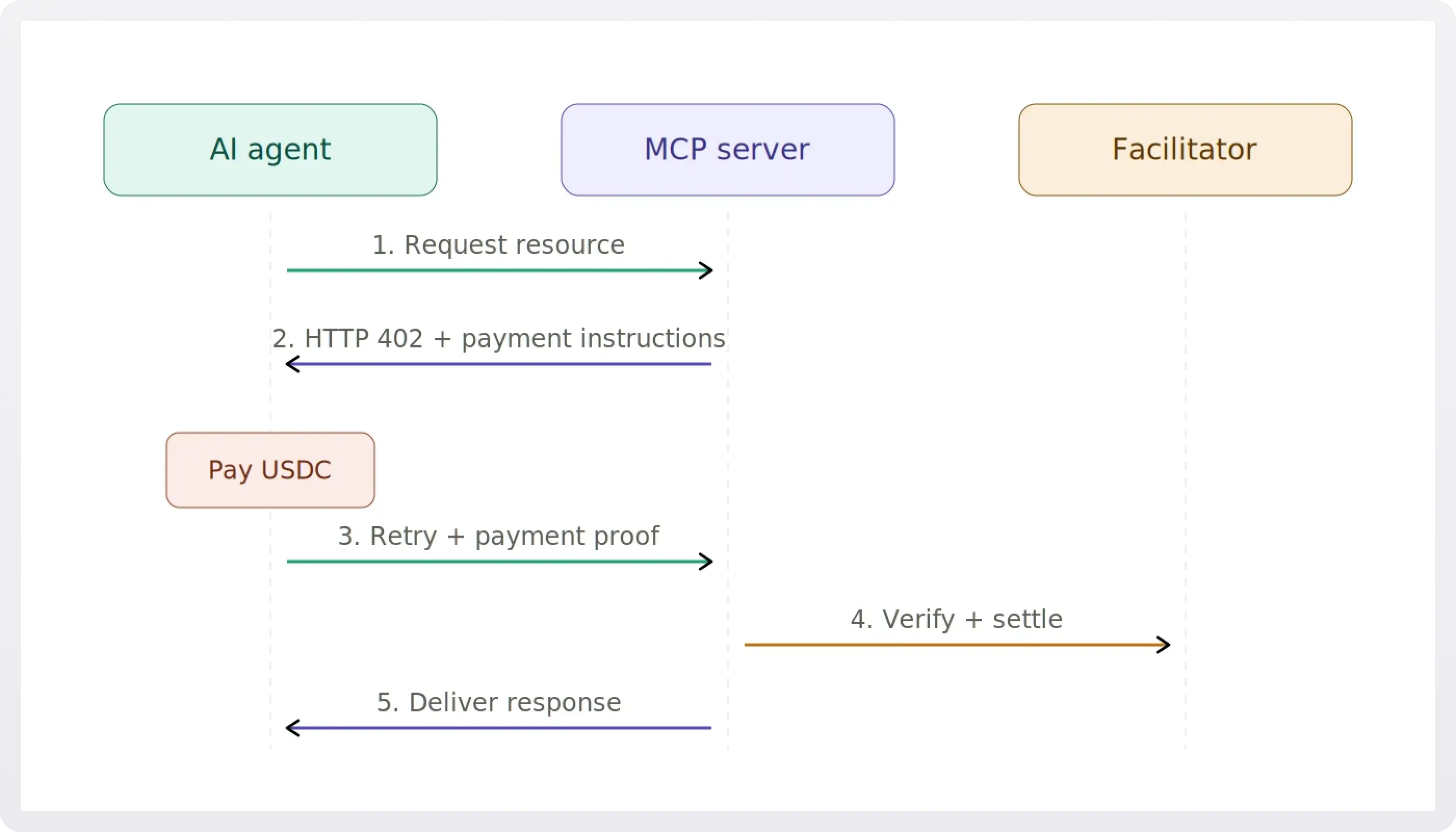
There is no need for accounts, API keys, or subscriptions. The payment receipt is the credential.
For MCP servers specifically, Vercel built x402-mcp: an npm package that wraps the x402 protocol into the Vercel AI SDK. It introduces the paidTool primitive, letting you declare a price on any MCP tool and require payment before execution. Here's what that looks like in practice:
That's a complete paid MCP tool: schema validation, pricing, and payment enforcement in one declaration. On the client side, a single wrapper enables automatic payment handling:
While x402-mcp is the most turnkey way to use x402 with MCP, the protocol itself is framework-agnostic and has middleware for Express, Hono, Next.js, and others.
!!x402 is not a complete payment platform. It does not handle subscriptions, invoicing, customer management, tax compliance, or chargeback disputes. It is a protocol-level primitive for per-request payments.!!
Stripe MPP (Machine Payments Protocol): The high-throughput, compliance-included one
MPP launched on March 18, 2026 alongside Tempo's mainnet. It was co-authored by Stripe and Tempo. Where x402 requires one blockchain transaction per request, MPP introduces sessions: an agent authorizes a spending limit upfront, then streams micropayments against that session continuously without a separate on-chain transaction for each call.
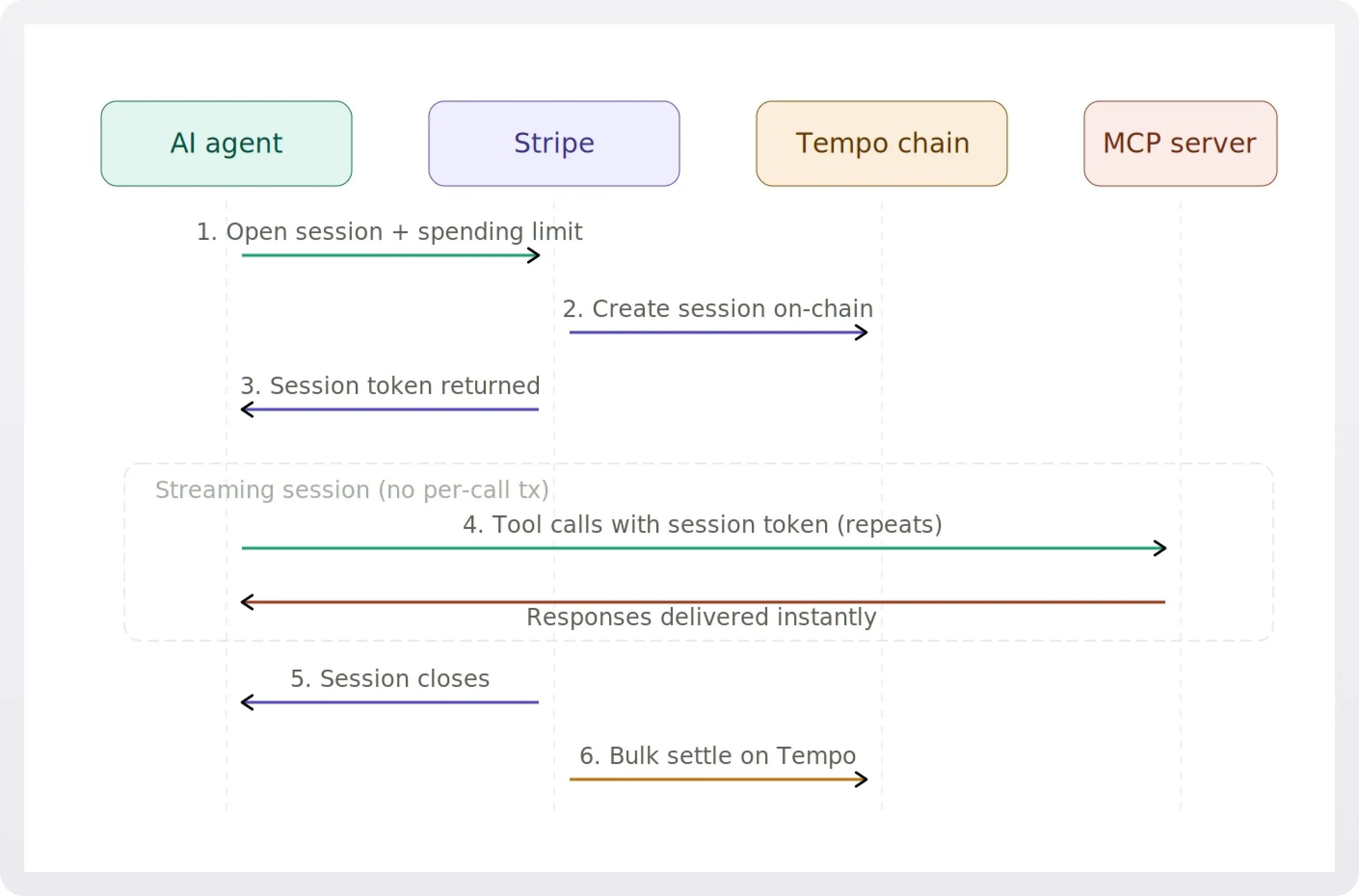
This matters for high-frequency scenarios. If your agent queries a data feed thousands of times per hour, you don't want to sign and broadcast a chain transaction each time. Sessions solve that by aggregating payments and settling in bulk.
Tempo's chain is purpose-built for this. It processes tens of thousands of transactions per second with sub-second finality and has no native gas token; fees are paid in stablecoins. MPP flows into Stripe's existing PaymentIntents API, so merchants get fraud detection (Radar), tax handling, and reporting out of the box.
MPP also works alongside Stripe's Shared Payment Tokens (SPTs), meaning an agent paying through MPP can use USDC on Tempo or a user's linked Visa card. That hybrid fiat + crypto capability is unique to this approach.
x402 vs. Stripe MPP: Head-to-head comparison
Developer experience
x402 has the lowest barrier to entry in the agent payments space. Using the x402-mcp package, you define a paidTool with a price, point to a wallet address, done. On the client side, wrapping the MCP client with withPayment() handles the 402 handshake automatically.
MPP requires a Stripe integration, which means more setup (SDK, dashboard, PaymentIntents). But if you're already on Stripe, adding MPP is closer to a configuration change than a replatform. Session management adds some complexity on the client side, but Stripe handles settlement, compliance, and reporting in return.
Pricing models
Both protocols target per-request and micropayment pricing, but they differ in execution.
x402 settles each request as a discrete on-chain payment. Simple, transparent, but it means every call incurs blockchain overhead (even if that overhead is tiny on Base).
MPP aggregates payments within a session and settles in bulk. This makes it more efficient for high-frequency scenarios where per-transaction overhead adds up over thousands of calls.
Cost structure
x402: Transactions on Base settle for fractions of a cent. No platform fees; just nominal blockchain network fees. A $0.01 API call costs roughly $0.011 total. Sub-penny pricing becomes economically rational.
MPP: Tempo has no native gas token; fees are paid in stablecoins and are designed to be negligible. Session-based aggregation further reduces per-call overhead. Because MPP settles into Stripe, merchants get Stripe's processing, but the on-chain leg is cheap.
Both are orders of magnitude cheaper than traditional card processing for small payments. The cost difference between x402 and MPP is minor; the bigger distinction is in what's included (MPP bundles compliance) versus what you build yourself (x402 leaves it to you).
Security and trust
This is where the two approaches diverge most for decision-makers.
- x402 security model: Payments are cryptographically signed and settled on-chain, providing finality and transparency. No chargebacks; once paid, it's settled. The flip side: if an agent overpays or pays a malicious endpoint, there's no built-in recourse. The V2 spec (December 2025) introduced dynamic payment routing and modular SDKs, which expand functionality but also introduce new attack surfaces. Dynamic routing means the server tells your agent where to send money, opening the door to recipient manipulation. The modular SDK introduces supply-chain risks through third-party plugins. Production deployments need: recipient allowlists, per-session and per-agent budget caps, rate limiting, chain validation, and monitoring for anomalous spending. Tools like PaySentry are emerging to fill this gap, but the space is still immature.
- Stripe MPP security model: Sessions provide built-in spending limits. Stripe's compliance stack (Radar fraud detection, PCI, tax) applies to MPP payments. SPTs scope credentials by merchant, time, and amount, preventing runaway agent spending. The tradeoff is dependence on Stripe and Tempo as intermediaries. You're trusting their infrastructure rather than building your own controls.
Ecosystem and adoption: a reality check
The institutional momentum behind both approaches is impressive. But the actual usage numbers tell a more tempered story.
- x402: Coinbase reports over 50 million cumulative transactions through its Agentic Wallets infrastructure. However, on-chain analysis paints a more nuanced picture: as of early March 2026, daily transaction volume was roughly 131,000 transactions and ~$28,000 in value, with a $0.20 average payment. Roughly half appeared to be testing or gamified activity rather than real commerce. Real production users include Neynar (social data queries), Hyperbolic (GPU inference), and Token Metrics (crypto analytics). The x402 Foundation (Coinbase + Cloudflare) and inclusion in Google's AP2 initiative provide strong institutional backing. Stripe also offers native x402 integration, so merchants can accept x402 payments through their existing Stripe dashboard.
- MPP: Launched March 18, 2026, just days ago. Tempo lists collaborations with Anthropic, DoorDash, Mastercard, Nubank, OpenAI, Ramp, Revolut, Shopify, Standard Chartered, and Visa. Over 100 services in the payments directory at launch, including Alchemy, Dune Analytics, and Merit Systems. It's too early for meaningful volume data, and "collaboration" at launch can mean anything from a signed letter of intent to live production traffic.
Both are early. The infrastructure is being laid by serious players, but agent payment volume at scale is still ahead of us, not behind us.
The hybrid path: Combining x402, MPP, and traditional billing
For many teams, the right answer isn't a single protocol. The most pragmatic architecture uses different payment paths for different audiences:
- x402 for autonomous agents making one-off or low-frequency calls (permissionless, no setup)
- MPP for high-frequency agent sessions that benefit from aggregation and Stripe's compliance
- Stripe traditional for human customers who want subscriptions, invoices, and dashboards
Here's what a hybrid middleware looks like in practice (pseudocode):
One middleware, multiple verification paths. Human teams get invoices and dashboards. High-frequency agents get session efficiency. One-off agents get permissionless access. No audience is locked out.
This is also Stripe's position: they support x402, MPP, and traditional billing through separate integration paths, all settling into the same merchant dashboard. Their strategy is to own the abstraction layer and let the protocols compete underneath. If you don't want to bet on a single protocol, Stripe as your settlement layer keeps your options open.
What this means if you're building an MCP server today
- x402 is the fastest way to start. With x402-mcp, the
paidToolabstraction is clean and MCP-native. If your tools do discrete, bounded work (search, lookup, transform, generate), putting a $0.001 to $0.01 price on each call is now a realistic monetization path with minimal code. - MPP is worth watching if you expect high-frequency agent traffic. If your MCP tools will be called hundreds of times per session (data feeds, monitoring, continuous queries), session-based aggregation avoids per-call blockchain overhead. The Stripe integration means you get compliance and fraud protection without building it yourself.
- You'll need to build operational scaffolding around x402 yourself. How do you handle refunds? Monitoring? Rate limiting for runaway agent spending? Key management? These are all your problem with x402. MPP delegates most of this to Stripe.
- The pricing model shift is real either way. Moving from subscriptions to per-request billing changes how you think about your product. You're no longer selling access; you're pricing individual units of work. This requires understanding your cost per call, your value per call, and the elasticity of demand at different price points. It's more like pricing a serverless function than pricing a SaaS seat.
- Your users need crypto wallets (for now). x402 requires USDC on Base or Solana. MPP requires USDC on Tempo (or fiat via SPTs). For developer-to-developer and agent-to-agent scenarios, this is increasingly normal. For mainstream adoption, wallet onboarding is still a friction point, though managed wallet solutions from Coinbase and others are closing the gap.
x402 and MPP FAQ
Will x402 actually replace API keys and subscriptions?
Not universally, and probably not soon. x402 eliminates the need for API keys in the specific case of autonomous, on-demand tool access. But subscriptions exist for a reason: they provide predictable revenue for providers and predictable costs for consumers. Enterprise buyers in particular value committed pricing and invoicing. What's more likely is that x402 opens up a new tier of access (casual, exploratory, agent-driven) that sits alongside, not instead of, existing billing. Think of it like the relationship between pay-per-view and a streaming subscription: different models for different consumption patterns.
How does the developer experience compare in practice?
For the narrow case of per-request MCP tool payments, x402 (via x402-mcp) is dramatically simpler. Five lines of server code, a one-line client wrapper, and you're collecting payments. MPP adds session management but gives you Stripe's full stack in return. The DX question is really: how much of the payments stack do you actually need? If the answer is "just charge per call and I'll handle the rest," x402 wins. If the answer is "charge per call with fraud protection, tax compliance, and reporting," MPP wins.
What are the real security risks of autonomous agent payments?
The core risk is that an agent with wallet access can spend money at machine speed, including on malicious or overpriced endpoints. For x402: V2's dynamic routing means the server tells your agent where to send money, which opens the door to recipient manipulation if you're not validating addresses. Session-based identity can be hijacked. The modular SDK introduces supply-chain risks through third-party plugins. Production deployments need recipient allowlists, per-session and per-agent budget caps, rate limiting, chain validation (to prevent gas-fee manipulation), and monitoring for anomalous spending patterns. MPP's session model mitigates some of this by design (built-in spending limits, Stripe Radar), but introduces its own trust dependency on Tempo and Stripe as intermediaries.
What about regulatory and tax implications?
x402 payments settle in USDC, which means you're receiving cryptocurrency. Depending on your jurisdiction, this has tax reporting implications (capital gains treatment, income recognition, reporting thresholds). You're also responsible for your own KYC/AML compliance if applicable. There is no IETF RFC for x402 yet, meaning multiple implementations could fragment. MPP settles through Stripe, which handles tax, compliance, and reporting automatically. If you're in a regulated industry, MPP gives you micropayment capability without the compliance burden of raw x402.
Is x402 only for crypto-native teams?
Increasingly, no. The protocol itself is payment-network agnostic and designed to support non-crypto payment methods in the future. But today, the production implementations settle in USDC on Base or Solana. Managed wallet solutions from Coinbase and others are lowering the crypto knowledge bar, and Stripe's own x402 preview means you can use familiar Stripe tooling to accept x402 payments. That said, if your team has zero crypto experience, expect a learning curve around wallet management, key security, and on-chain monitoring. MPP may be the easier on-ramp since it wraps the crypto in Stripe's familiar interface.
What does the competitive landscape look like beyond x402 and MPP?
Google's AP2 (Agents Payment Protocol) uses a mandate-based system where users delegate spending authority with fine-grained controls. Visa and Mastercard are developing their own agentic payment standards and plan to make them mandatory for AI agent transactions. Academic research (e.g., the A402 paper from March 2026) is proposing more sophisticated channel-based protocols to address x402's atomicity limitations. The space is early and fragmented; expect consolidation, but also expect x402's openness and MPP's Stripe backing to keep both relevant.
How real is the adoption? Should I wait?
The volume is still small. x402's daily on-chain activity as of early March 2026 was roughly 131,000 transactions and ~$28,000 in value, with a meaningful portion being testing activity. MPP launched days ago; it's too early for real data. But the infrastructure is being laid by serious players (Coinbase, Cloudflare, Stripe, Tempo, Google, Visa). The question isn't whether agent payments will matter; it's when. Starting with x402 is low-cost and low-commitment (a few lines of code, a wallet address). You can layer on MPP or traditional Stripe as your needs evolve. There's little downside to being ready when the agents show up.
The bottom line
The agent payments landscape as of March 2026 has two purpose-built protocols competing for different strengths:
- x402 is the simplest, most open, and most permissionless option. Best for: per-request micropayments, autonomous agent access, no-vendor-lock-in architectures, and teams comfortable managing their own security and compliance.
- Stripe MPP is the high-throughput option with enterprise compliance built in. Best for: high-frequency agent sessions, hybrid fiat + crypto payments, and teams that want Stripe's fraud detection, tax handling, and reporting without building it themselves.
These are not mutually exclusive. Stripe supports both (plus traditional billing) through different integration paths, settling into a single dashboard. The most forward-looking teams will treat payment protocol selection the way they treat compute infrastructure: pick the right tool for each workload, and design your system to support more than one.
The future of agent payments is not one protocol to rule them all. It's a layered model, and the best teams will choose their payment infrastructure as deliberately as they choose everything else in their stack.
Payments are only half the story. What about auth?
This article covers how agents pay for MCP tools. But before an agent can pay, it needs to prove who it is and what it's allowed to do. Authentication and authorization for MCP servers is the other critical infrastructure layer, and it's evolving just as fast.
WorkOS MCP Auth provides OAuth 2.1 authorization for MCP servers out of the box: PKCE, scopes, tool-level permissions, and fine-grained access control for agentic workflows. If you're building MCP tools that need to know who's calling (not just that they've paid), it handles the auth complexity so you can focus on the tools themselves.